本文原创,转载请注明出处: http://maosidiaoxian.iteye.com/blog/1683990
在上个月我曾发了一篇Activity劫持与用户防范的文章(http://maosidiaoxian.iteye.com/blog/1623016),在里面介绍了由于Android设计上的缺陷而导致的钓鱼漏洞,并且也在文末介绍了用户防范的方法(原创)。
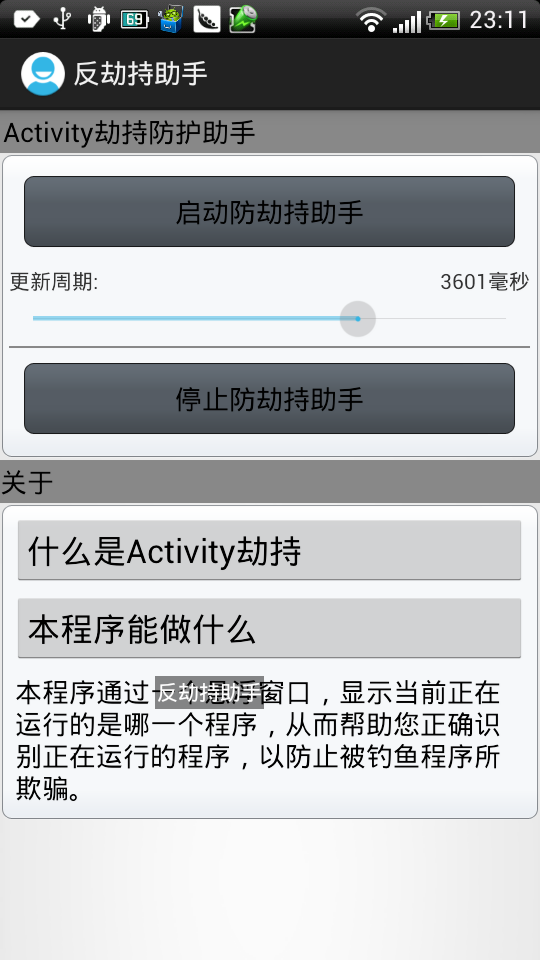
然而,如果真的爆发了这种恶意程序,我们并不能在启动程序时每一次都那么小心去查看判断当前在运行的是哪一个程序。因此,前几个星期花了一点时间写了一个程序,叫反劫持助手。原理很简单,就是获取当前运行的是哪一个程序,并且显示在一个浮动窗口中,以帮忙用户判断当前运行的是哪一个程序,防范一些钓鱼程序的欺骗。
在这一次,由于是“正当防卫”,就不再通过枚举来获取当前运行的程序了,在manifest文件中增加一个权限:
<uses-permission android:name="android.permission.GET_TASKS" />
然后启动程序的时候,启动一个Service,在Service中启动一个浮动窗口,并周期性检测当前运行的是哪一个程序,然后显示在浮动窗口中。
程序截图如下:
其中Service代码如下:
/* * @(#)AntiService.java Project:ActivityHijackingDemo * Date:2012-9-13 * * Copyright (c) 2011 CFuture09, Institute of Software, * Guangdong Ocean University, Zhanjiang, GuangDong, China. * All rights reserved. * * Licensed under the Apache License, Version 2.0 (the "License"); * you may not use this file except in compliance with the License. * You may obtain a copy of the License at * * http://www.apache.org/licenses/LICENSE-2.0 * * Unless required by applicable law or agreed to in writing, software * distributed under the License is distributed on an "AS IS" BASIS, * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. * See the License for the specific language governing permissions and * limitations under the License. */package com.sinaapp.msdxblog.antihijacking.service;import android.app.ActivityManager;import android.app.Notification;import android.app.Service;import android.content.Context;import android.content.Intent;import android.content.pm.PackageManager;import android.content.pm.PackageManager.NameNotFoundException;import android.os.Bundle;import android.os.Handler;import android.os.IBinder;import android.os.Message;import android.util.Log;import com.sinaapp.msdxblog.androidkit.thread.HandlerFactory;import com.sinaapp.msdxblog.antihijacking.AntiConstants;import com.sinaapp.msdxblog.antihijacking.view.AntiView;/** * @author Geek_Soledad ([email protected]) */public class AntiService extends Service { private boolean shouldLoop = false; private Handler handler; private ActivityManager am; private PackageManager pm; private Handler mainHandler; private AntiView mAntiView; private int circle = 2000; @Override public IBinder onBind(Intent intent) { return null; } @Override public void onStart(Intent intent, int startId) { super.onStart(intent, startId); startForeground(19901008, new Notification()); if (intent != null) { circle = intent.getIntExtra(AntiConstants.CIRCLE, 2000); } Log.i("circle", circle + "ms"); if (true == shouldLoop) { return; } mAntiView = new AntiView(this); mainHandler = new Handler() { public void handleMessage(Message msg) { String name = msg.getData().getString("name"); mAntiView.setText(name); }; }; pm = getPackageManager(); shouldLoop = true; am = (ActivityManager) getSystemService(Context.ACTIVITY_SERVICE); handler = new Handler( HandlerFactory.getHandlerLooperInOtherThread("anti")) { @Override public void handleMessage(Message msg) { super.handleMessage(msg); String packageName = am.getRunningTasks(1).get(0).topActivity .getPackageName(); try { String progressName = pm.getApplicationLabel( pm.getApplicationInfo(packageName, PackageManager.GET_META_DATA)).toString(); updateText(progressName); } catch (NameNotFoundException e) { e.printStackTrace(); } if (shouldLoop) { handler.sendEmptyMessageDelayed(0, circle); } } }; handler.sendEmptyMessage(0); } private void updateText(String name) { Message message = new Message(); Bundle data = new Bundle(); data.putString("name", name); message.setData(data); mainHandler.sendMessage(message); } @Override public void onDestroy() { shouldLoop = false; mAntiView.remove(); super.onDestroy(); }}
浮动窗口仅为一个简单的textview,非此次的技术重点,在这里省略不讲。
当然,从以上代码也可以看出本程序只能防范通过Activity作为钓鱼界面的程序,因为它是通过运行的顶层的Activity来获取程序名称的,对WooYun最近提到的另一个钓鱼方法它还是无能为力的,关于这一点将在下次谈。
本文原创,转载请注明出处: http://maosidiaoxian.iteye.com/blog/1683990